AbsoluteTelnet / SSH is a telnet and SSH client for Windows! A secure flexible SSH client with SFTP file transfer and rock-solid emulations that is suitable for developers, administrators, or deployment across the enterprise. It includes the industry standard SSH protocols to secure terminal session data across insecure environments such as the internet. Its new tabbed interface is a favorite among AbsoluteTelnet users, and new features are being added all the time! If you need unrelenting performance and unmatched features, then AbsoluteTelnet is what you’ve been looking for. Download it now and take it for a spin!!
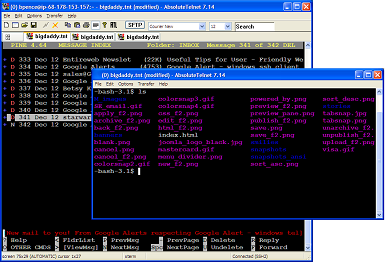
How to connect AbsoluteTelnet/SSH to a Synology NAS device
How to Connect AbsoluteTelnet/SSH to a Synology NAS using SFTP Connecting AbsoluteTelnet/SSH to Synology NAS…
Compiling opendkim on Amazon Linux 2023
While configuring a new server for sendmail, it is a good practice to install DKIM…
Compatible Algorithms
Compatible algorithms are chosen at connection time from the algorithm lists enabled and supported by…
Supported Algorithms
AbsoluteTelnet/ssh supports an extensive set of crypto algorithms to connect to just about ANY modern…
Deprecated Algorithms
From time to time, crypto algorithms are deprecated for use in SSH. Absolute discourages use…
ASCII File Send
Here is a script implementation of a feature I get asked for a lot: ASCII…